CyberArk and the Future of Identity Security in Cloud Environments

Cloud adoption has unlocked speed and scale for organizations everywhere. But it has also redrawn the security landscape. With traditional perimeters disappearing, identity is now the new control point. Every user, application, and machine identity must be verified and protected against threats. CyberArk Training in Bangalore delivers the capabilities businesses need to secure identities across cloud, hybrid, and on-premises environments helping them reduce risk and move with confidence.
Identity as the New Security Perimeter
In cloud-first environments, access is no longer defined by firewalls it’s defined by identity. CyberArk Online Training applies least privilege and continuous verification to ensure only trusted identities gain access to critical resources.
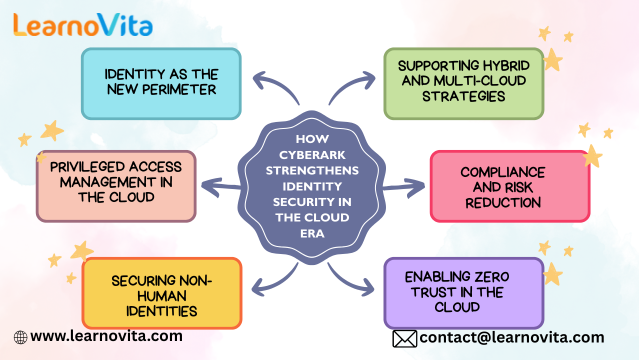
Protecting Privileged Access
Privileged accounts remain the top target for attackers. CyberArk reduces risk by:
-
Vaulting and securing sensitive credentials.
-
Automating password and key rotation.
-
Monitoring and recording privileged activity.
-
Detecting and blocking unusual behavior in real time.
This stops stolen credentials from escalating into full-scale breaches.
Managing Machine Identities
Automation and cloud-native development mean non-human identities now outnumber people. CyberArk automates secrets management, ensuring that APIs, microservices, and bots authenticate securely enabling DevOps speed without creating vulnerabilities.
Operationalizing Zero Trust
Zero Trust requires “never trust, always verify.” CyberArk makes this actionable with:
-
Enforced least privilege everywhere.
-
Adaptive authentication and continuous validation.
-
Just-in-time access to remove standing privileges.
The result: attackers have fewer opportunities to exploit compromised identities.
Simplifying Compliance
Regulations such as GDPR, HIPAA, and PCI DSS demand strict access control. CyberArk streamlines compliance with built-in auditing, monitoring, and reporting reducing complexity while strengthening oversight.
Consistency Across Clouds
Most organizations operate in multi-cloud and hybrid setups. CyberArk provides a single, unified approach to securing identities across AWS, Azure, Google Cloud, and on-premises systems closing gaps and simplifying management.
Conclusion
In the cloud era, identity is the foundation of security. CyberArk equips organizations to protect both human and machine identities, safeguard privileged access, and bring Zero Trust to life. With CyberArk, businesses can embrace the cloud securely and confidently.
- Art
- Causes
- Crafts
- Dance
- Drinks
- Film
- Fitness
- Food
- Jeux
- Gardening
- Health
- Domicile
- Literature
- Music
- Networking
- Autre
- Party
- Religion
- Shopping
- Sports
- Theater
- Wellness