From Recon to Exploits: 10 Ethical Hacking Tools You’ll Use

Ethical hacking, also known as white-hat hacking, is the practice of identifying vulnerabilities in systems before malicious hackers can exploit them. It plays a vital role in cybersecurity, helping organizations safeguard sensitive data, networks, and applications. For anyone starting in cybersecurity or even experienced professionals having a solid toolkit of ethical hacking tools is essential. Here are ten widely used tools every Ethical Hacking Online Course should know.
1. Nmap
Nmap (Network Mapper) is a highly versatile tool for network discovery and security auditing. It allows ethical hackers to scan networks, identify active devices, detect open ports, and determine running services. Nmap’s OS detection and service fingerprinting features make it indispensable for mapping a network’s attack surface before conducting more in-depth tests.
2. Metasploit Framework
Metasploit is a powerful exploitation framework that enables testers to safely simulate real-world attacks. It comes with a vast library of pre-built modules and payloads, which allows ethical hackers to validate vulnerabilities and demonstrate the potential impact of security flaws. Metasploit is a critical tool for penetration testing and vulnerability assessments.
3. Wireshark
Wireshark is a network protocol analyzer that captures and inspects live network traffic. Ethical hackers use it to analyze packets in detail, spot insecure transmissions, and troubleshoot network issues. Its ability to provide deep insights into network behavior makes it an essential tool for both testing and forensic investigations.
4. Burp Suite
Burp Suite is a comprehensive platform for web application security testing. Its intercepting proxy allows testers to monitor and manipulate HTTP/S requests, while features like the scanner and intruder help detect common vulnerabilities such as SQL injection and cross-site scripting (XSS). Burp Suite is a go-to tool for web application penetration testing.
5. Aircrack-ng
Aircrack-ng is a specialized suite for auditing wireless networks. It captures packets, performs attacks on network protocols, and can crack WEP and WPA/WPA2 passwords. Software Training Institute Used in controlled, authorized environments, Aircrack-ng helps testers assess Wi-Fi security effectively.
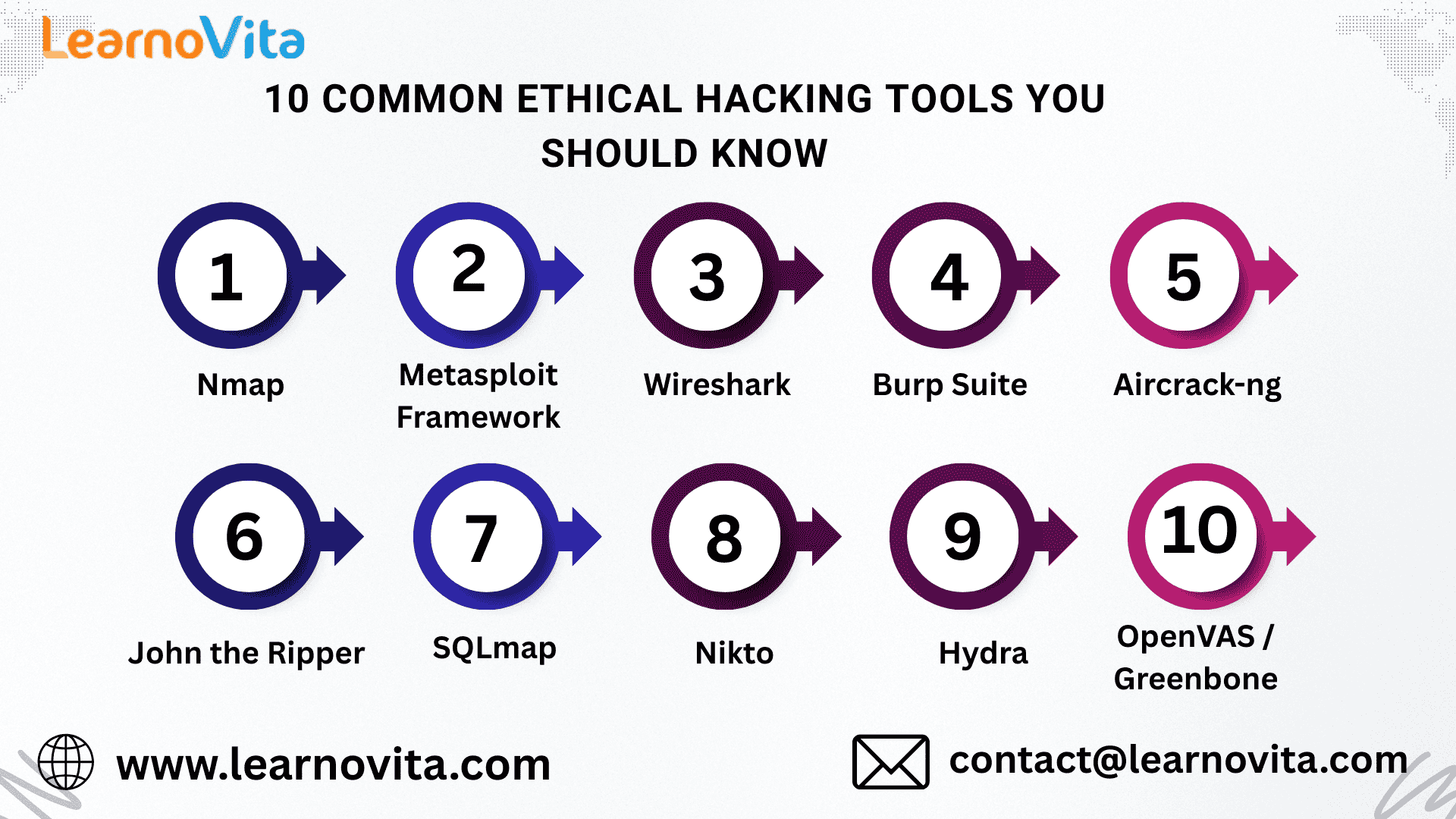
6. John the Ripper
John the Ripper is a password-cracking tool used to test the strength of user credentials. It supports multiple hashing algorithms and employs dictionary attacks, rule-based methods, or brute-force techniques. Ethical hackers use it to identify weak passwords and improve organizational security policies.
7. SQLmap
SQLmap automates the detection and exploitation of SQL injection vulnerabilities in web applications. It can enumerate databases, extract sensitive data, and even gain system access under certain conditions. SQLmap significantly speeds up database security testing and vulnerability validation.
8. Nikto
Nikto is a web server scanner that quickly identifies outdated software, misconfigurations, and known vulnerabilities. While simple and straightforward, it provides a fast baseline assessment of web server security and helps uncover common issues that might otherwise be overlooked.
9. Hydra
Hydra is a high-speed network login cracker supporting multiple protocols such as SSH, FTP, and HTTP. It is used to test authentication strength and account security in ethical hacking exercises, ensuring that password policies and lockout mechanisms are effective.
10. OpenVAS / Greenbone
OpenVAS, part of Greenbone Vulnerability Management, is an open-source vulnerability scanner. It conducts comprehensive scans of networks and systems, identifies security weaknesses, and generates detailed reports. OpenVAS is particularly valuable for full-scale security audits.
Conclusion
Ethical hacking tools are powerful, but they must always be used responsibly. Always obtain proper authorization before testing any system. By combining these ten tools with a structured approach reconnaissance, scanning, testing, and reporting—you can help organizations identify and fix vulnerabilities before they are exploited. Mastering these tools is a critical step toward becoming a skilled ethical hacker and protecting the digital world.
- Art
- Causes
- Crafts
- Dance
- Drinks
- Film
- Fitness
- Food
- Игры
- Gardening
- Health
- Главная
- Literature
- Music
- Networking
- Другое
- Party
- Religion
- Shopping
- Sports
- Theater
- Wellness